Kappa-error plot, the convex hull, and the Pareto optimal set of pairs... | Download Scientific Diagram

Concurrence of form and function in developing networks and its role in synaptic pruning | Nature Communications
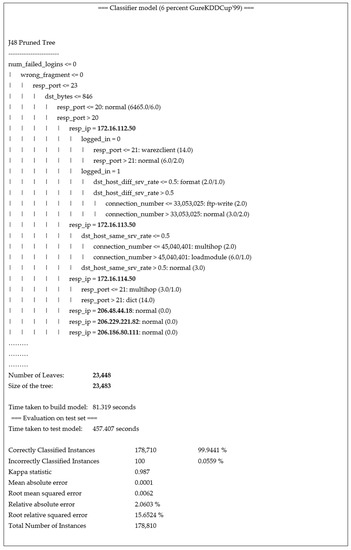
Electronics | Free Full-Text | Adoption of IP Truncation in a Privacy-Based Decision Tree Pruning Design: A Case Study in Network Intrusion Detection System

Comparison of Kappa coefficient between pruning and trial-and-error... | Download Scientific Diagram
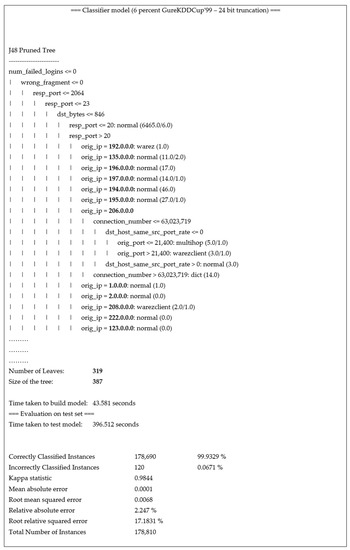
Performance Evaluation of GINI Index and Information Gain Criteria on Geographical Data: An Empirical Study Based on JAVA and Python | SpringerLink
Detecting Depression in Speech: A Multi-classifier System with Ensemble Pruning on Kappa-Error Diagram

Diversity-accuracy diagrams in terms of the Kappa degree-of-agreement. | Download Scientific Diagram

Kappa-Error diagrams for Leveraging Bagging and Online bagging (bottom)... | Download Scientific Diagram
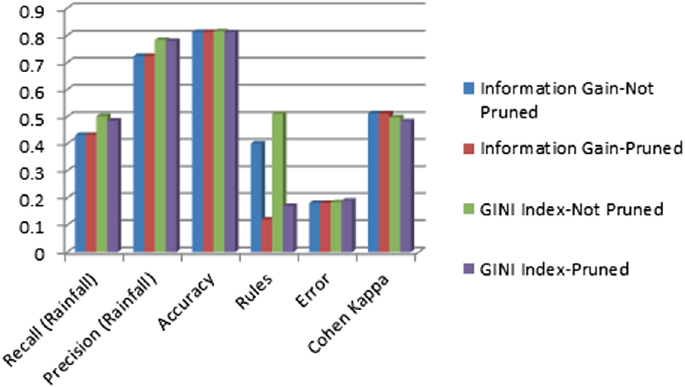
IJMS | Free Full-Text | Red Light Irradiation In Vivo Upregulates DJ-1 in the Retinal Ganglion Cell Layer and Protects against Axotomy-Related Dendritic Pruning